• https://media.defcon.org/DEF..
• Electromagnetic spectrum and
radioelectric spectrum -
Javier Luque Ordóñez
• Electromagnetic Radiation
- Katherine Rojas Monsalvo
- Universidad pontificia Bolivariana
- Specialization in telecommunications
- Bucaramanga - 2009
• The Electromagnetic Spectrum and
its Applications
- Bernardo Fontal
• Heinrich Hertz Research
on Electromagnetic Waves
- Pedro W. Lamberti - FaMAF
- UNC - Ciudad universitaria Córdoba.
• The Antennas - R. Brault & R. Piat
- Editorial Paraninfo 1998
• Practical Antenna Handbook Fourth Edition
- Joseph J. Carr
• Through-The-Earth (TTE) Communications
for Underground Mines
- Josua Peña Carreño, Lucas Sousa e Silva,
Sávio Oliveira de Almeida Neves,
Leonardo Aguayo, Adoniran Judson Braga,
André Noll Barreto,
and Luis Guilherme Uzeda Garcia


Governments and the private sector around the world are known to spend billions of dollars on countermeasures to protect their communication systems from eavesdropping and interference. But many other times they themselves use devices to disrupt the communication channels of third parties. A police department, for example, in some cases uses jammers , to interrupt the communication of criminals, as well as in prisons to prevent inmates from using smuggled cell phones. The military uses jammers to disrupt radar communications, prevent remote IED activation or radio communications. The private sector uses jammers to disrupt boardroom espionage and protect VIPs from explosive devices.
What if there was a way to communicate freely without knowing the point of origin and immune to jamming devices?
This question was asked by Chris Rock at the start of his talk entitled Killer Hertz at DEFCON 2022.

Introduction
To begin this post it is necessary to have an idea of electromagnetic compatibility ( EMC), in any manual without going into much detail and in several pages of the web we find the following definition:
This is a branch of electrical, electronic and telecommunications engineering that studies the mechanisms to eliminate, diminish and prevent the effects of coupling between an electrical or electronic equipment and its electromagnetic environment, even from its design, based on standards and regulations, ensuring the reliability and safety of all types of systems in the place where they are installed and under a specific electromagnetic environment/surrounding environment (i.e. vegetation, animals or people). With respect to human health, this discipline addresses the issue of possible harm caused by certain electronic equipment.
In addition, EMC sets standards to prevent some highly sensitive or vital equipment from being affected by electromagnetic pollution, as is the case of medical implements and/or devices or auxiliary equipment in aeronautics.
With this small definition, a new question arises:
The answer is yes, and we call that electronic countermeasure, or ECCMthis can be an electrical or electronic device designed, and following the previous example, to deceive or circumvent radars, sonars or other detection systems such as infrared or laser. It can be used both offensively and defensively to prevent the "enemy" from identifying its targets. It is commonly used by air forces to protect aircraft from missile attacks. They have also been deployed on warships and recently on advanced combat vehicles to deceive laser or infrared guided missiles.
Beyond its military use, how could we use an ECCM to communicate bypassing all these protections (communication being understood as the transmission and reception of information, not just a voice channel)?
Chris explains that using a custom made Tx/Rx, and taking advantage of the Earth's crust, an H-field Near Field Communication (NFC) channel could be generated covering 1 to 11 km in the sub 9 kHz range to communicate encrypted messages in a jammed/controlled environment, in his demo he manages to trigger an explosive object remotely bypassing the "guarded" channels. If this last paragraph seemed a bit more advanced to you, we are going to detail some concepts below, if not, you can jump directly to the "Earth and Sea as Hardware" section.
Electromagnetic Waves
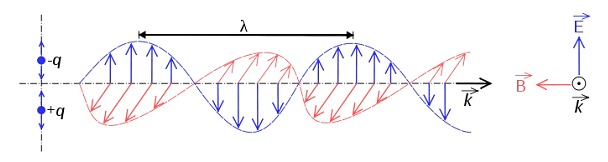
Electromagnetic waves are produced by the oscillation or acceleration of an electric charge; these waves have electric and magnetic components and their theoretical aspects are related to the waveform solution supported by Maxwell's equations.
The electromagnetic wave is the way in which energy (electromagnetic radiation) propagates through space thanks to the electrons that release them under certain conditions; thanks to this, technologies that can send information through space such as Bluetooth, Wi-Fi, AM, FM, among others, are possible.
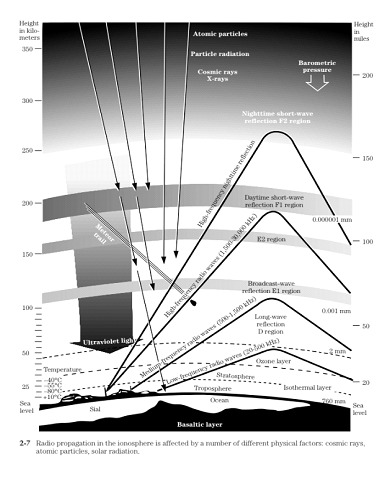
Unlike mechanical waves, electromagnetic waves do not need a material medium to propagate and travel in a vacuum at a speed of c = 300,000 km/s. All radiations of the electromagnetic spectrum exhibit the typical properties of wave motion, such as diffraction and interference. Wavelengths range from billionths of a meter to many kilometers. The wavelength (λ) and frequency (f) of electromagnetic waves, related by the expression λ-f = c, are important in determining their energy, visibility, penetrating power and other characteristics.
Characteristics of an electromagnetic wave
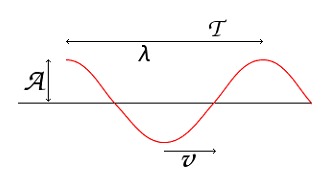
Amplitude (A):It is the measure of the magnitude of the maximum disturbance of the medium produced by the wave. The amplitude defines the power of the wave.
Wavelength (λ):
The distance between the start and end points of a cycle as the wave travels in a given medium.
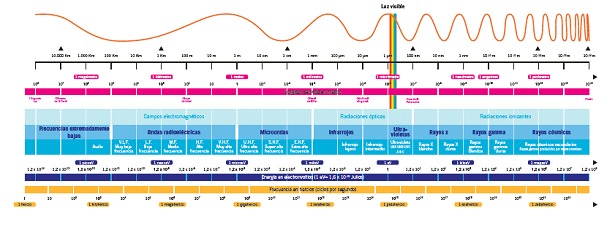
Electromagnetic spectrum
The electromagnetic waves, suitably treated and modulated (usually by varying the amplitude, phase and/or frequency of the original wave) can be used for the transmission of information, giving rise to a form of telecommunication.
Nowadays, electromagnetic waves of different frequencies are massively used for the transmission of information by guided media (twisted pair, coaxial cable, optical fiber, etc.) and by unguided media (usually air or vacuum). The frequencies used in each case depend on their behavior in the different materials used as transmission media, as well as on the desired transmission speed.
In the particular case where the propagation of electromagnetic waves is carried out by unguided means, this form of telecommunication is called radiocommunication or wireless communication. Thus, the part of the electromagnetic spectrum used primarily for radio communications is called the radio spectrum.
On previous occasions we addressed this same concept, but with another perspective, I invite you to read Trojan detection in hardware approached from the visible spectrum, and side channel attack consisting of a reversing based on the magnetic field created by some encrypted Eeproms.
In summary, the spectrum can be divided as follows:

Land and Sea as Hardware
Subradio or subhertz waves are those belonging to band 3 and below, i.e. frequencies below 3 kHz. According to ITU-R nomenclature, it includes ULF, SLF and ELF waves. Sub-radio waves are hardly used in communications, as they have clear disadvantages.
Their transmission rate is very low, due to the fact that they are very small bandwidths, so unmanageable antennas are needed. The optimum power of an antenna for a frequency is presented for antenna lengths equal to half the wavelength of the signal to be emitted, for example, for a frequency of 10 Hz, an antenna length of 15,000 km would be needed for optimum radiation.
Due to the electrical conductivity of seawater, submarines are isolated from the vast majority of electromagnetic communications. However, very low frequency signals (ELF and SLF, few tens of Hz) can penetrate much deeper.
This fact, together with the possibility of reducing the size of the antennas, due to electrical elongation phenomena, has been used in the military field for communications with submarines.
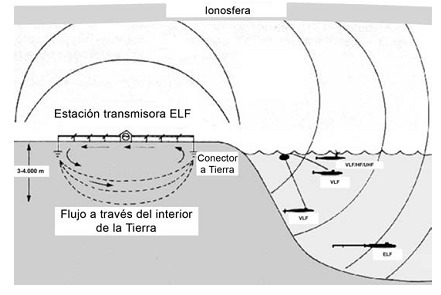
In practice, these communications have been one-way and very short messages, e.g., instructing the submarine to surface at shallow levels to establish communications in some other way. The Earth emits ELF waves naturally due to the resonant cavity formed between the ionosphere and the surface. The Earth's ELF waves are initiated by electric rays oscillating electrons in the atmosphere. In uses other than radio communications for electromagnetic waves in the ELF band, the most important is the transport of electrical energy: the frequencies of 50 and 60 Hz are used all over the world to provide electricity to any point on the planet.
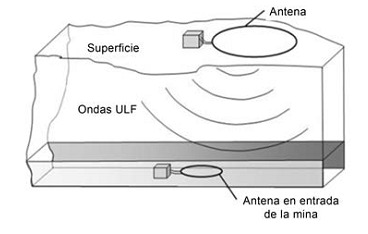
ULF band frequencies are common in the Earth's magnetosphere. This band is used for communication in mines ( TTE –Through The Earth–system, limited to short text messages in a paging service, due to the existing low bandwidth), as it can penetrate the earth's crust.
For this same reason, it has been used in the military for secure communications across the ground. This ULF band is also sometimes used by radio amateurs for limited range communications.
Proof of concept
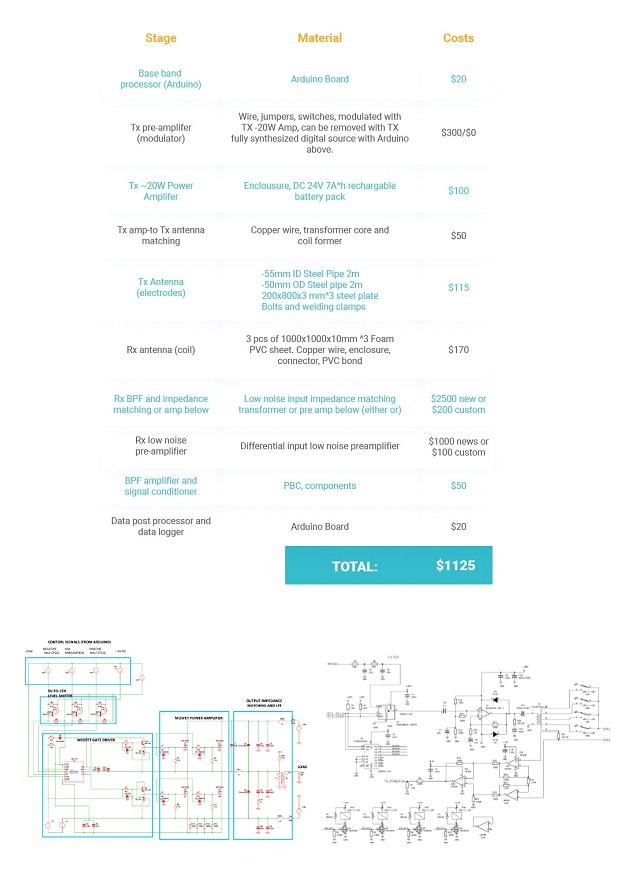
Now that we have reviewed all the concepts and have knowledge of the TTE system, we can refocus on the statement that Chris gave us.
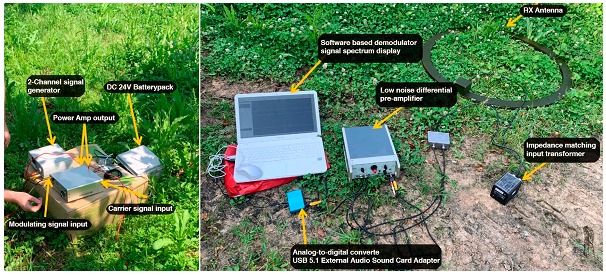
For this purpose, we provide a list with the elements necessary to establish such a channel and the schematic to do it:

Conclusion and Use Cases
After several simulations in software such as ANSYS HFSS 3D to simulate electromagnetic behavior RES2Mod for geophysical simulations and CST Studio a high performance EM analyzer, several conclusions could be reached that encouraged the construction of the POC that we saw above, (We recommend reading the full presentation where these results are discussed in more depth). The test achieved the following results and characteristics according to the author:
In the original video of this exhibition you can see how to activate an explosive charge at a distance without being detected or uninterrupted by known jammers this could compromise any type of infrastructure or even human lives, but beyond this implementation and although this channel can be used only to send one-way messages of a few characters as we saw in the example of submarines, it can be implemented in as many ways as you can imagine, from the agricultural sector, for example as a possible substitute for Lora Wan, to beacons for espionage practices. Once again we can highlight the value of reinventing relatively simple technologies created many years ago, since many of these technologies escape modern standards and security frameworks. It is very likely that if an implementation is not yet thought out, it is even less likely to be thought out how to protect against it.
